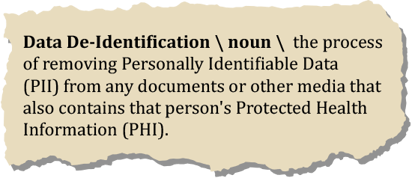
What is Data De-Identification?
Data de-identification is the process of removing Personally Identifiable Data (PII) from any documents or other media that also contains that person's Protected Health Information (PHI). De-identification is the fastest and simplest way to ensure compliance and identification security on methods of communication that could be accessed by the public or outsiders.
 The biggest benefit is that the de-identified data can be stored (PHI with PII removed) in any system; the rules and code that is linked to this data doesn't need to adhere to HIPAA.
The biggest benefit is that the de-identified data can be stored (PHI with PII removed) in any system; the rules and code that is linked to this data doesn't need to adhere to HIPAA.
And in an age where everything is stored online, data de-identification is becoming increasingly important.
But what do you need to know about de-identifying data? How do you actually de-identify data?
Here Are 5 Important Facts to Know About Data De-Identification:
#1 - It’s Required Under HIPAA's De-Identification Standards for Health Information
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) Privacy Rule requires organizations to de-identify their data to remain in accordance with the law.
 HIPAA outlines two specific methods that satisfy the health information de-identification standard, including Expert Determination and Safe Harbor.
HIPAA outlines two specific methods that satisfy the health information de-identification standard, including Expert Determination and Safe Harbor.
That’s why so many healthcare organizations invest a considerable amount of time and money into data de-identification.
However, as you’ll learn below, this capability is useful for more than just healthcare information.
#2 - Data De-Identification Is Useful for More Than Just Personal Data
When you think of data de-identification, you probably think of personal records: someone’s data is separated from their other data, usually protected health information. This prevents them from being personally identified.
That’s the case with a lot of data de-identification processes. However, it’s not the case with all of them.
The truth is, data de-identification can be useful for more than just personal data, including some of the following circumstances:
 Businesses involved in statistical surveys (like industry surveys) may wish to have their data de-identified
Businesses involved in statistical surveys (like industry surveys) may wish to have their data de-identified- Mining companies may wish to de-identify the spatial location of mineral deposits
- Environmental protection agencies may want to de-identify data linked to endangered species
There are countless other examples where de-identified data can be useful.
In short, it’s a valuable way to protect more than just individual healthcare patients – it can be used across industries for all different types of benefits.
#3 - How To De-Identify Data from a Data Set
You know why data de-identification is important. But how do you actually de-identify data?
 Typically, it involves using an intelligent software to remove identifiers, names, addresses, gender, date of birth, and other identifying information from datasets.
Typically, it involves using an intelligent software to remove identifiers, names, addresses, gender, date of birth, and other identifying information from datasets.- Sometimes, that data is removed entirely. In other cases, the data is coded or encrypted. Some de-identification services also change data values or aggregate data to remove the personal connection.
- But what if you want to reuse that data at a future point – like for inclusion in a future study? That’s where de-identifying data can get tricky.
- In this situation, researchers need to walk through a minefield of legislation, policies, and ethical guidelines to ensure they’re doing everything the right way.
#4 - HIPAA’s Expert Determination Versus Safe Harbor Method: Which Should a Covered Entity Use?
Up above, we mentioned that HIPAA requires one of two ways of de-identifying data for a covered entity (health care provider, health care clearinghouse or health plan) to perform, including Expert Determination and Safe Harbor.
Expert Determination involves applying statistical or scientific principles to the data. This ultimately leads to a very small risk that the anticipated recipient could identify the individual.
Safe Harbor, on the other hand, requires the removal of 18 types of identifiers (like all geographic subdivisions below the state level). With Safe Harbor, there’s no chance that the residual information can be used to identify the individual.
#5 - A Better Solution: How to De-Identify Your Data and Eliminate Identification Risks
BIS offers a solution called Grooper that can help companies like yours with de-identifying information and data.
 The technology is particularly helpful for health information companies (HIPAA compliance), colleges and universities (FERPA compliance), financial institutions (PCI standards), and government/public records (SSNs).
The technology is particularly helpful for health information companies (HIPAA compliance), colleges and universities (FERPA compliance), financial institutions (PCI standards), and government/public records (SSNs).
Grooper is an information processing platform that offers the following deidentification benefits for your business:
Grooper has the same functionality offered by legacy document capture platforms – but with new features that make it even more useful.
Worried about a data breach? Eliminate identification risks - it's easy with Grooper.
Learn how we empowered fast and easy data de-identification at a large nation wide credit union. Download our case study: